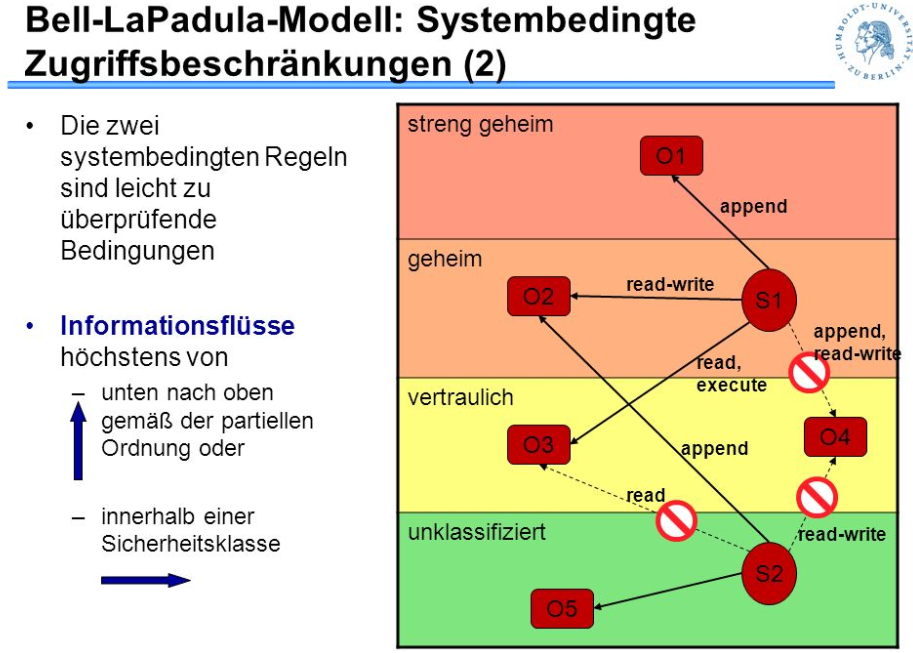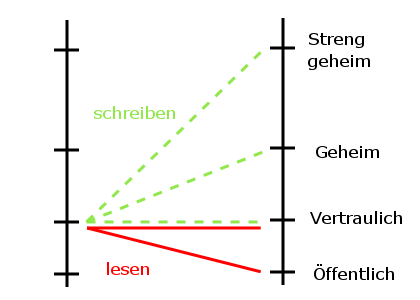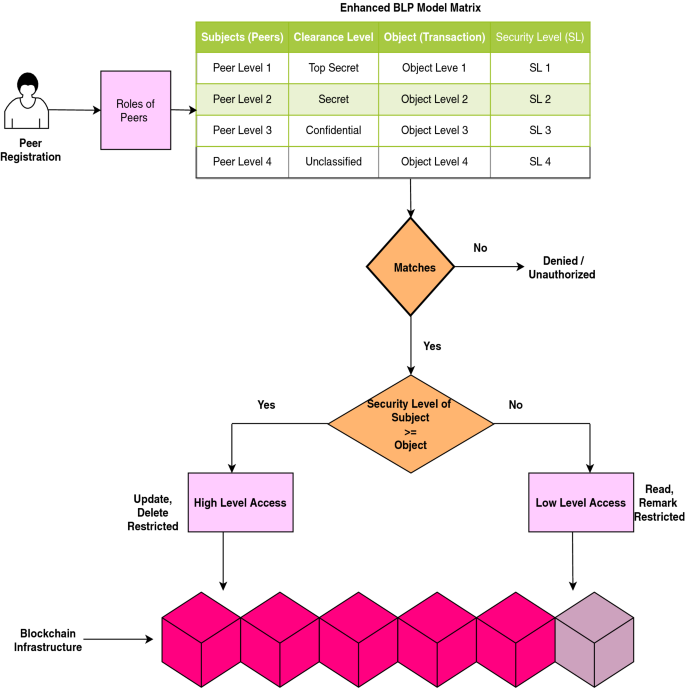
Scalable and secure access control policy for healthcare system using blockchain and enhanced Bell–LaPadula model | SpringerLink

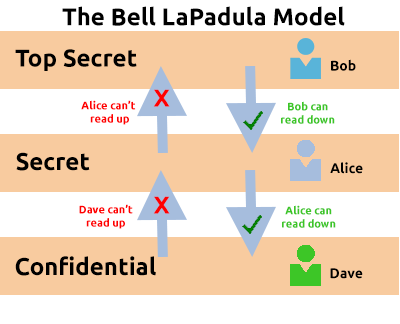
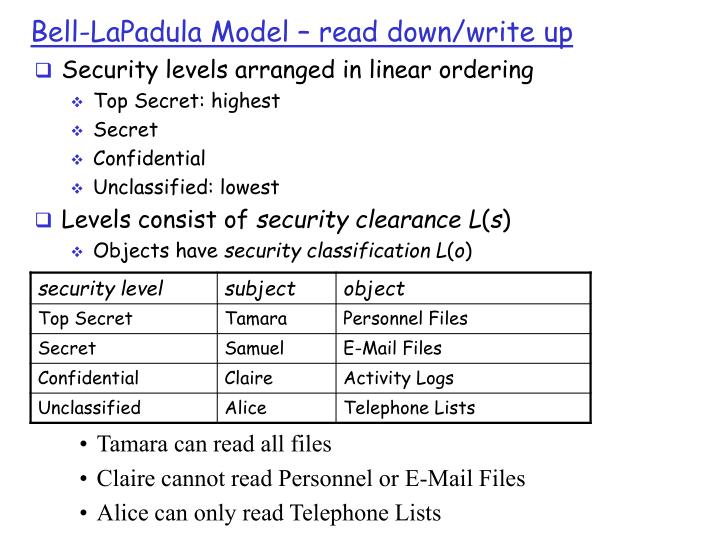
Secured Information Access based on Bell LaPadula model A Case of Novel Publishing Company | Semantic Scholar

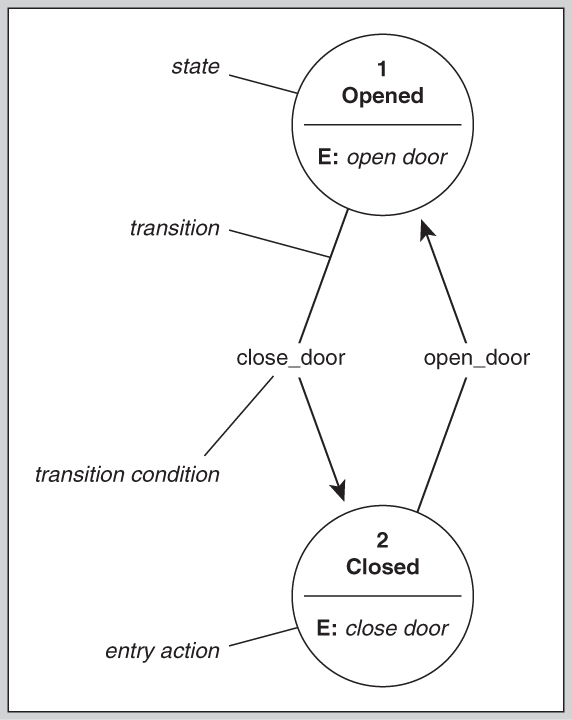
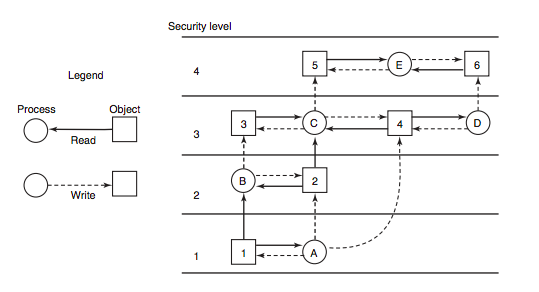
CISSP PRACTICE QUESTIONS – 20210401 by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu