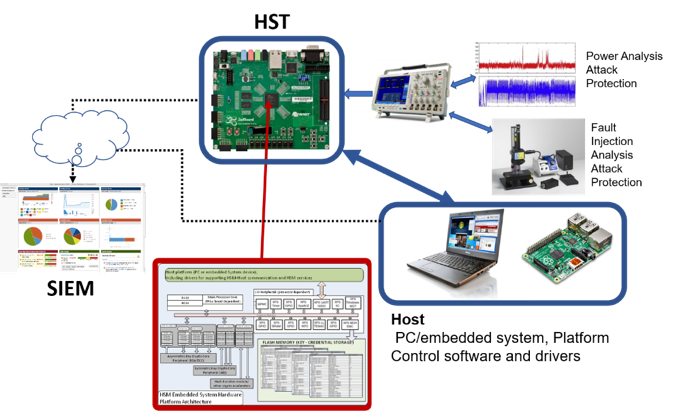
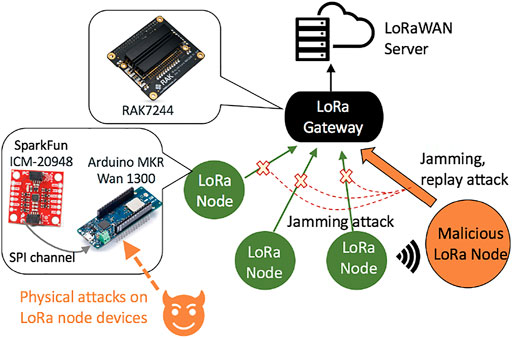
Hardware-based attacks based on different entities in the semiconductor... | Download Scientific Diagram

Hardware security knowledge in terms of the hardware-based attacks,... | Download Scientific Diagram

Research on evaluation techniques for detecting LSI vulnerabilities - Research| Hardware security research team | Cyber physical security reserch cente
Malwarebytes na Twitteru: "An interesting thing we've seen are some major #hardware attacks. How remembers #Spectre & #Meltdown? - @MalwarebytesCSO #cybersecurity #infosec https://t.co/0ARwnu44cZ" / Twitter

![PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fac9e722cd47fa28222a53bb4d624a42d0d0d04/3-Figure2-1.png)
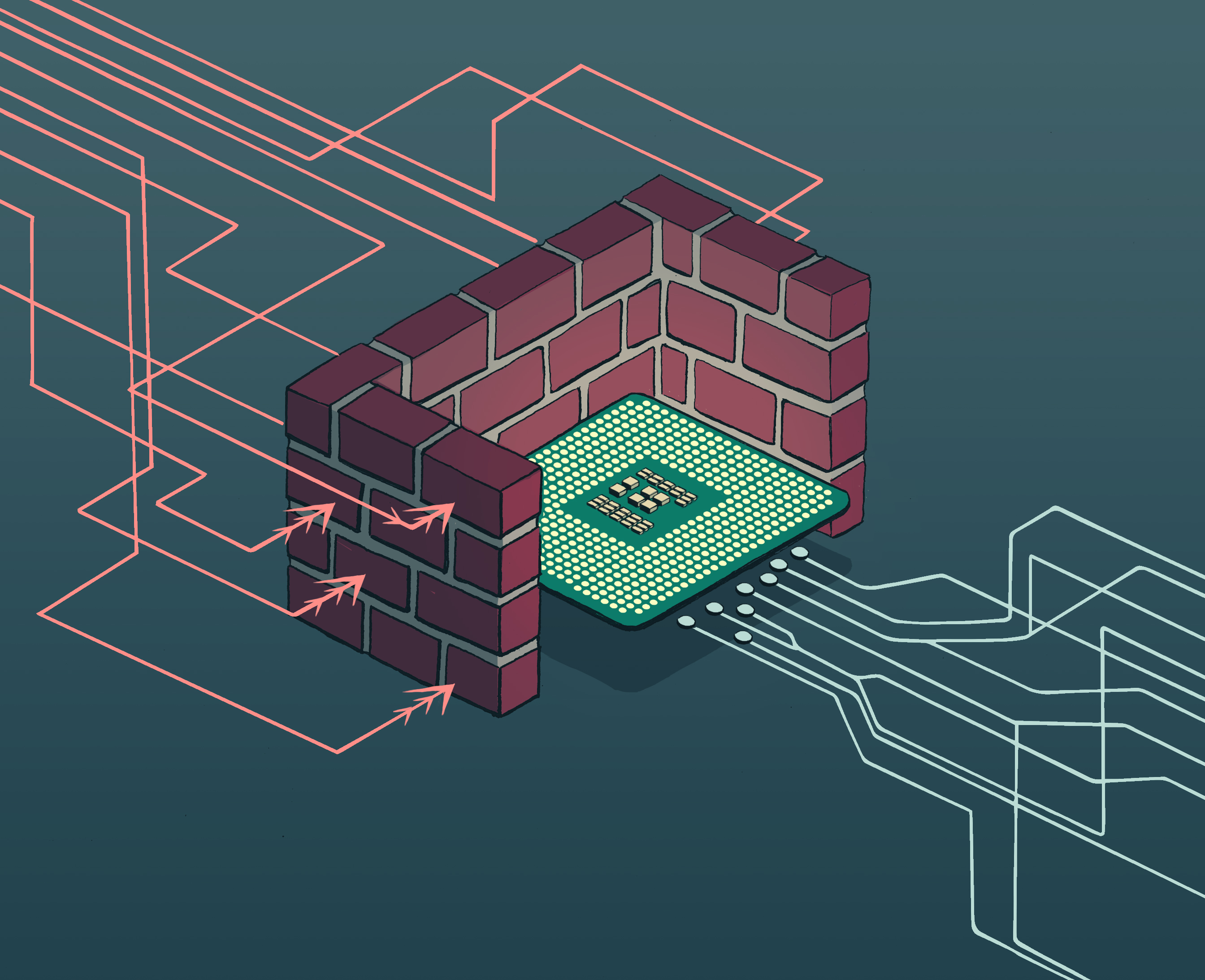
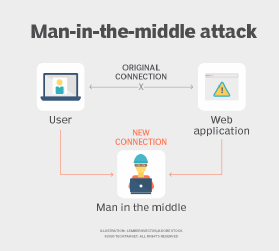







![PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fac9e722cd47fa28222a53bb4d624a42d0d0d04/5-Figure3-1.png)



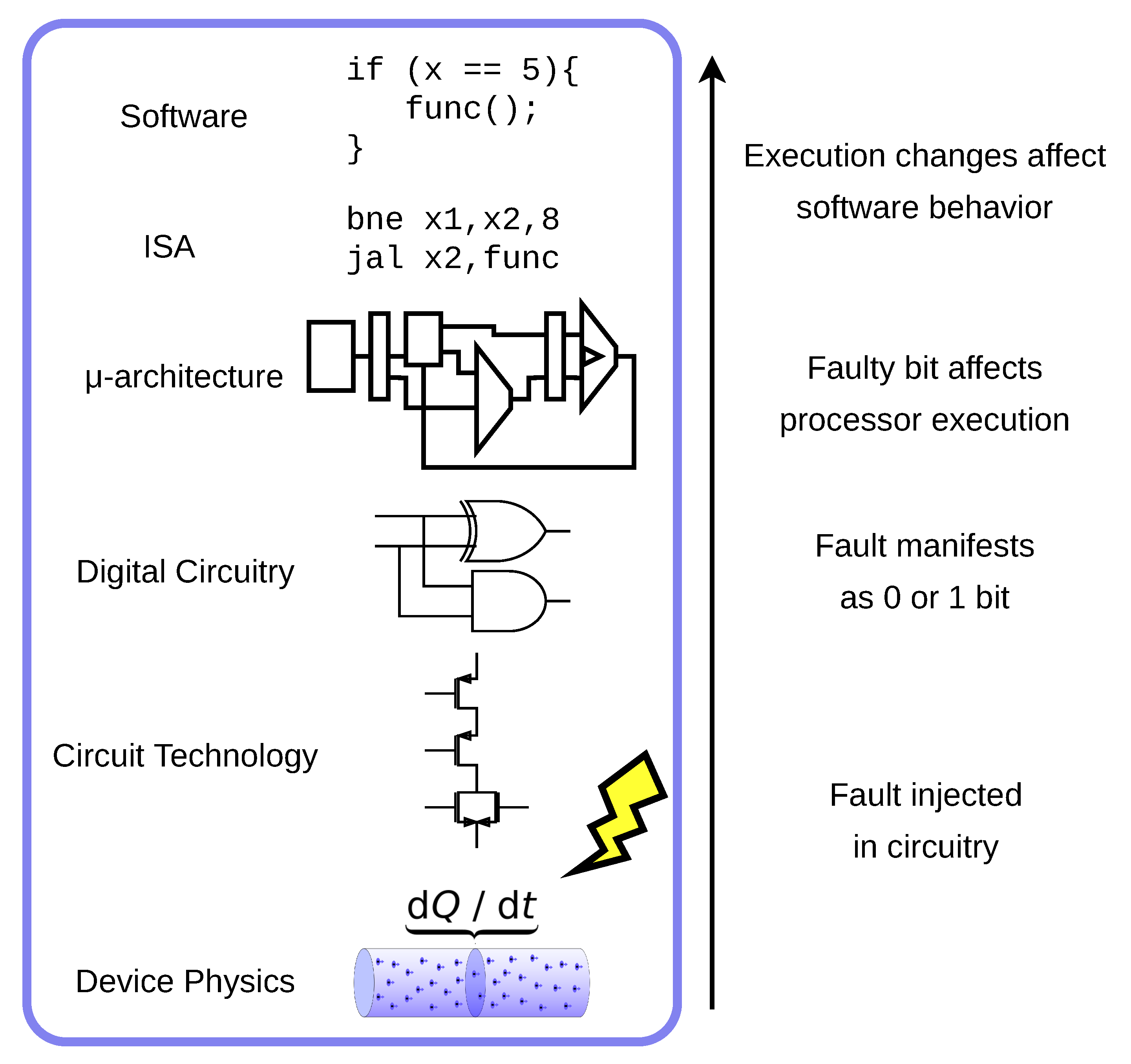
![PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar PDF] Hardware Security, Vulnerabilities, and Attacks: A Comprehensive Taxonomy | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1fac9e722cd47fa28222a53bb4d624a42d0d0d04/7-Figure4-1.png)